What Is Employment Identity Theft and How Does It Impact Hiring?
Someone applies for a job using a stolen identity, or a synthetic one engineered to look real and pass verification. The resume checks out. The interview goes smoothly. The background check passes.
Then they get access.
Remote hiring, AI-assisted interviews, and identity manipulation have made it easier for fraudulent candidates to blend in and harder for companies to detect them before it’s too late.
Most organizations don’t realize there’s a problem until access has already been granted.
What Is Employment Identity Theft?
Employment identity theft is when someone uses a false, stolen, or manipulated identity to get hired.
This can include:
- Using stolen personal information
- Creating synthetic identities that appear legitimate
- Posing as a real person
- Operating under multiple personas across platforms
In some cases, the goal is financial fraud. In others, it’s access to systems, data, and internal environments.
How Employment Identity Theft Happens
Modern employment identity theft is structured and intentional. It often involves multiple layers of deception designed to pass hiring processes and blend in as legitimate candidates.
Common tactics include:
- Fake personas: Fabricated identities with resumes, portfolios, and online presence designed to appear legitimate
- Stolen identities: Real individuals whose information is reused or manipulated
- AI-assisted interviews: Candidates using real-time tools to generate answers during interviews
- Multiple identities: Different versions of the same candidate appearing across platforms or applications
In more advanced cases, these tactics are coordinated to place individuals inside organizations at scale.
Real-World Example: DPRK Remote Worker Schemes
Employment identity theft is not theoretical. It is already being used in large-scale operations.
Investigations have shown that North Korean IT workers use stolen or synthetic identities to secure remote jobs at Western companies. These workers often rely on U.S.-based facilitators to receive equipment, establish infrastructure, and maintain the appearance of legitimate employment.
In one case, a candidate applying for a senior technical role appeared highly qualified, but subtle inconsistencies raised concern. Further investigation revealed:
- Resumes that mirrored job descriptions too closely
- Conflicting identity details across platforms
- Use of VoIP numbers and recently created email accounts
- AI-assisted responses during interviews
What initially looked like a strong candidate was later tied to a broader network of fraudulent remote workers operating under false identities.
What Employment Identity Theft Looks Like During Hiring
On paper, the candidate looks ideal. They bring a strong resume, loaded with relevant experience, and give a confident interview performance. But small signals begin to surface.
Before the Interview
Some indicators appear during the application and screening process:
- Limited or recently created online presence
- Suspicious email patterns or generic account formats
- Repetitive resumes or portfolio structures across applicants
- Profile images that appear altered or synthetic
During the Interview
Other signals emerge during live interactions:
- Answers that sound polished but lack depth
- Difficulty handling unexpected or unscripted questions
- Inconsistencies between interview responses and prior materials
- Signs of assisted or externally generated responses, including glancing away to a different screen
After Hiring
In some cases, clear indicators appear after access has already been granted:
- Performance that does not match interview capability
- Use of unauthorized remote access tools
- Inconsistencies in onboarding or shipping information
- Avoidance of real-time collaboration or team interaction
Individually, many of these signals may seem harmless. Together, they paint a very different picture.
Most hiring processes are built to confirm information, not question whether the identity behind it is real. Resumes can be polished. Interviews can be assisted. Background checks only validate the information they are given.
On paper, everything checks out. That’s the problem.
Business Impact of Employment Identity Theft
Hiring the wrong person is one thing. Hiring someone using a false or stolen identity is something else entirely.
The impact can include:
- Unauthorized access to systems and sensitive data
- Intellectual property theft
- Regulatory and compliance exposure
- Reputational damage
- Loss of trust among existing employees
In some cases, a single fraudulent hire can create risk across internal systems, customer environments, and third-party relationships.
Understand Who You Are Hiring
Employment identity theft is designed to look legitimate. Resumes check out. Interviews go smoothly. Background checks pass.
Nisos Employment Shield helps organizations investigate suspicious candidates, validate identity authenticity, and uncover risk signals that traditional screening often misses.
Whether you’re hiring for privileged access, remote technical roles, or other sensitive positions, analyst-led investigations can help surface inconsistencies before they become a larger security problem.
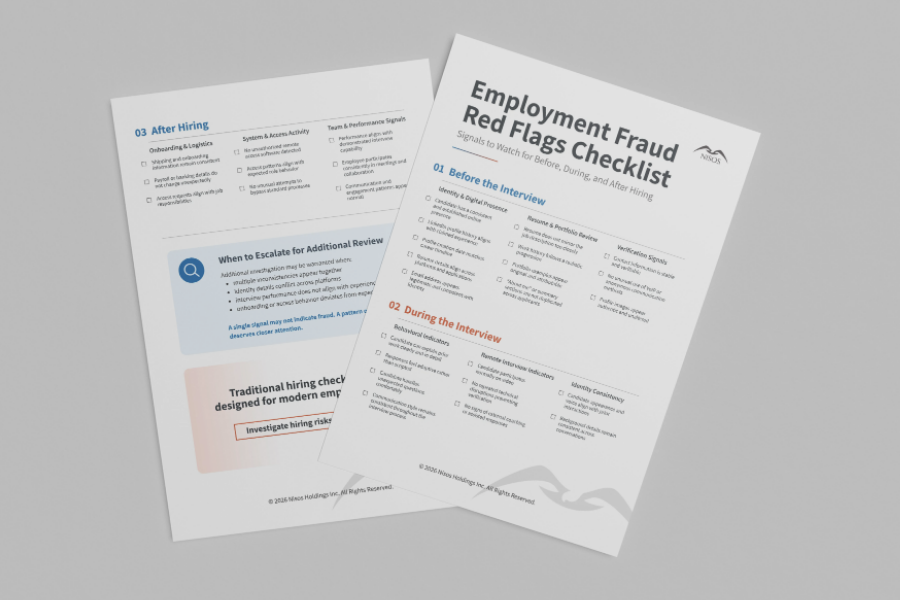
Download the Employment Fraud Red Flags Checklist to help your team identify warning signs before access is granted.
Frequently Asked Questions (FAQs) on Employment Identity Theft
What is employment identity theft?
How does employment identity theft happen?
Why is employment identity theft difficult to detect?
What are common signs of employment fraud?
How can organizations reduce employment fraud risk?
About Nisos®
Nisos is a trusted digital investigations partner specializing in unmasking human risk. We operate as an extension of security, risk, legal, people strategy, and trust and safety teams to protect their people and their business. Our open source intelligence services help enterprise teams mitigate risk, make critical decisions, and impose real world consequences. For more information, visit: https://nisos.com.