Your Digital Footprint Exposure: What’s Public and Why It Puts You at Risk
That exposure is not just a privacy issue. It can create real security risks when personal information is easy to access and exploit.
Your Digital Footprint is Bigger Than You Think
Whether you’re a CEO, a celebrity, or just someone who values their privacy, your digital footprint is likely much larger and more revealing than you realize. Every online interaction, property purchase, or app download contributes to a composite picture that can be exploited by those with malicious intent.
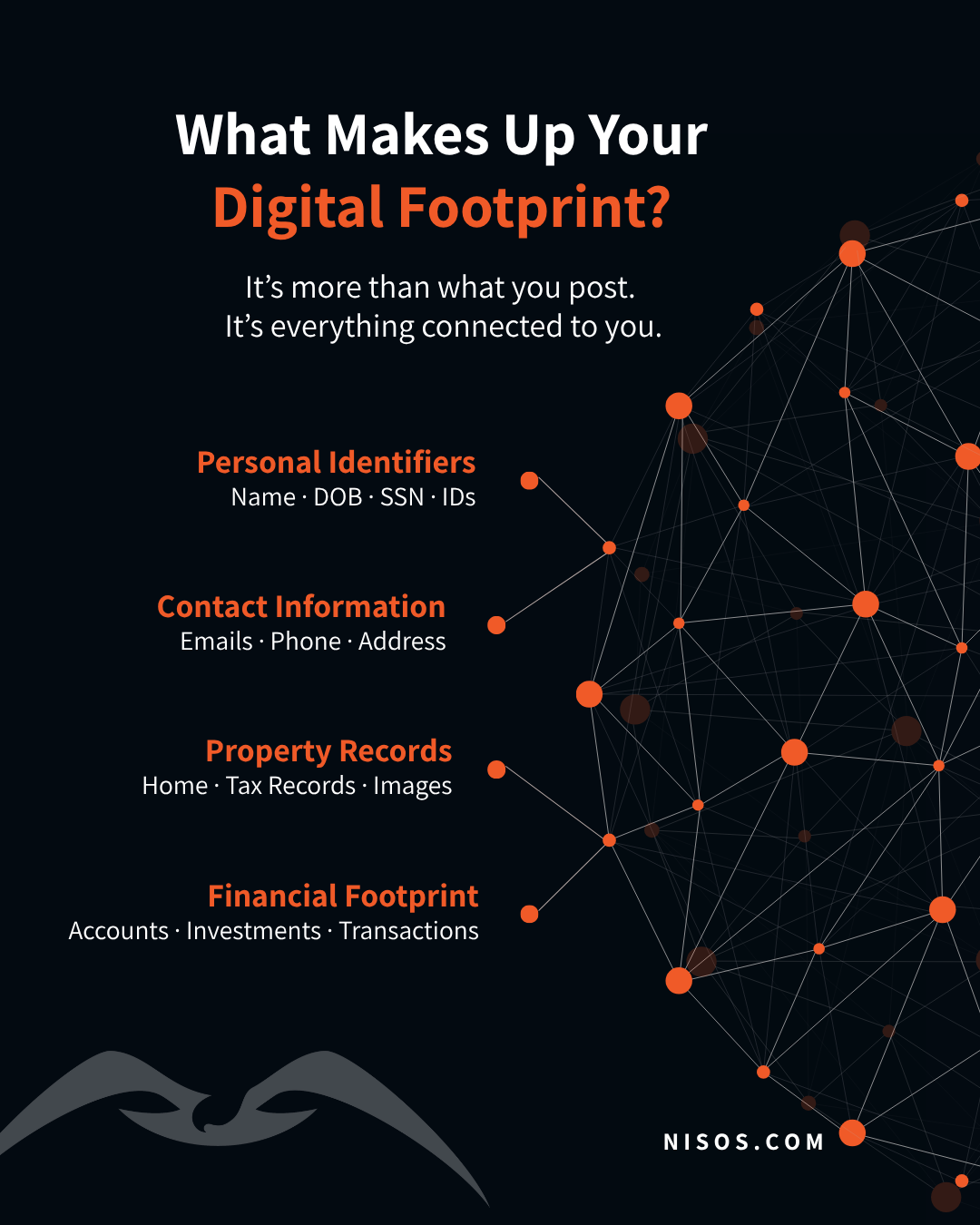
What Information Makes Up Your Digital Footprint?
Your digital footprint isn’t just your social media profiles. It’s a complex web of interconnected information that includes:
Personal Identifiers: Your full legal name, date of birth, Social Security number, driver’s license details, passport information, and professional license numbers
Contact Information: All your email addresses (both work and personal), phone numbers, mailing addresses, and digital messaging accounts
Property Records: Home addresses, property tax information, mortgage records, and even exterior and interior images of your property that are publicly accessible
Financial Footprints: Details about bank accounts, investment portfolios, charitable donations, and public records of financial transactions
The alarming reality? For executives, our research shows that 98% have property information visible online (including exterior images for 92% of them), and 100% have had email data exposed in breaches. Similar patterns likely extend beyond the boardroom to most of us, high-profile or not.
Not All Exposure Carries the Same Risk
Not all exposed information is equally dangerous. Some data points are inconvenient. Others can be used immediately for targeting, fraud, or impersonation.
Understanding the risk levels of different types of exposed information is crucial:
Critical Risk (Tier 1): Information that enables physical targeting or direct financial fraud, like home addresses with property images and Social Security numbers
High Risk (Tier 2): Information that facilitates targeted social engineering, such as dates of birth or personal email addresses
Moderate Risk (Tier 3): Information that builds comprehensive profiles, including employment history and family connections
Contextual Risk (Tier 4): Information that seems harmless alone but creates risk when combined with other data, like vacation announcements or routine check-ins
The Risk You’re Not Thinking About: Your Family
Here’s something that catches many people off guard: 30% of executives’ family members publicly share geolocation and pattern-of-life information online. Even if you’re careful about your own digital presence, your family members might be inadvertently exposing details about your life, schedule, and vulnerabilities.
How This Information Gets Used Against You
In our interconnected digital ecosystem, your information is constantly being “shared, aggregated, and exploited” across data brokers, public records repositories, and social media platforms. Without a systematic approach to identifying and removing this information, you’re left vulnerable to increasingly sophisticated threats.
Consider this: freely available personal information or social media posts revealing future locations provide threat actors with everything they need to target you effectively. What might seem like an innocent vacation post could be providing a roadmap for those with malicious intent.
How to Take Control of Your Digital Footprint
Understanding your digital exposure is the first step toward protection. A structured approach to assessing your digital footprint should include:
- Identification: Documenting all your personal identifiers across public records, data broker sites, and social media
- Exposure Analysis: Evaluating which information is publicly accessible and how easily others can obtain it
- Relationship Mapping: Identifying connections between you and family members, colleagues, and organizations that could provide additional access points
- Vulnerability Assessment: Determining which combinations of exposed information create the greatest security risks based on your unique profile
- Monitoring Implementation: Establishing ongoing surveillance of critical exposure points to detect new information leakage
Remediation Planning: Developing a strategic approach to removing or protecting the most critical information first
Start Reducing Your Digital Exposure Today
While this might seem overwhelming, you don’t have to navigate digital exposure alone. Our comprehensive Executive Protection Digital Hygiene Playbook provides detailed guidance for identifying and addressing your digital footprint vulnerabilities.
Whether you’re a high-profile individual concerned about targeted threats or simply someone who values their privacy in an increasingly exposed world, understanding and managing your digital footprint has never been more important.
Download our free playbook today to take the first step toward reclaiming control of your personal information and protecting yourself from digital exposure risks.
Frequently Asked Questions (FAQs) on Digital Footprint Exposure
Why is digital footprint exposure a security concern?
Can I fully remove my information from the internet?
How does personal data become publicly available?
What steps can I take to reduce my digital footprint?
Why does digital footprint exposure increase over time?
About Nisos®
Nisos is a trusted digital investigations partner specializing in unmasking human risk. We operate as an extension of security, risk, legal, people strategy, and trust and safety teams to protect their people and their business. Our open source intelligence services help enterprise teams mitigate risk, make critical decisions, and impose real world consequences. For more information, visit: https://nisos.com.
