Research
Exposing a Fraudulent DPRK Candidate: How Nisos Identified a Suspected North Korean Operative
Executive Summary
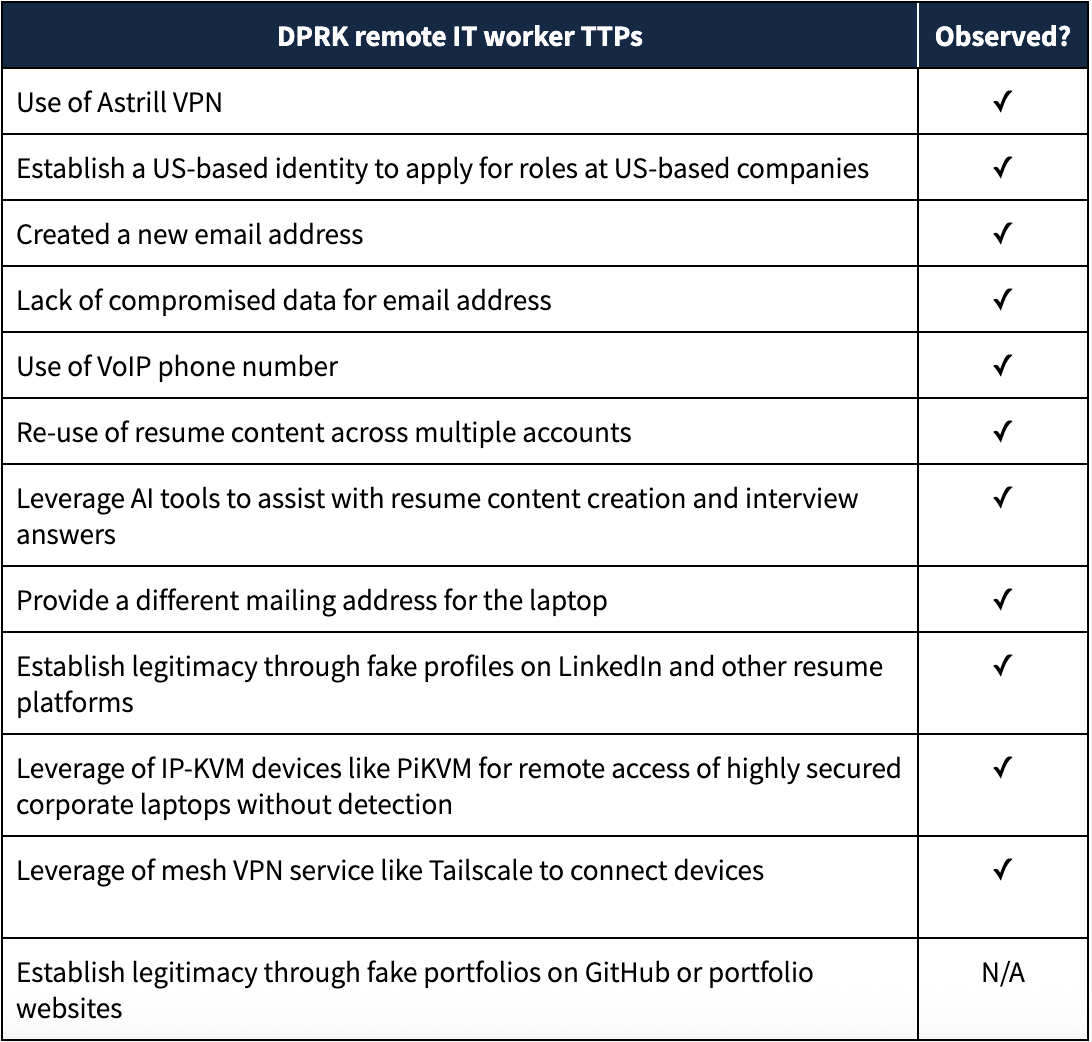
Since early 2023, Nisos has provided our clients with critical insights and conducted OSINT (Open-Source Intelligence) pre-employment and insider risk investigations to mitigate the threat of North Korean (DPRK) IT worker employment schemes. In June 2025, we used a combination of pre-employment OSINT due diligence and targeted interview questions to expose a suspected DPRK operative, who applied for a remote Artificial Intelligence (AI) architect role at Nisos. The operative unsuccessfully used stolen personally identifiable information (PII), a newly created email, and an AI-created resume to pose as a Florida-based lead AI architect and senior full stack developer. Nisos subsequently identified an employment fraud network involving the IT worker, which included a laptop farm located in Florida. Our investigation of the laptop farm identified that DPRK IT workers leverage Raspberry Pi-based KVM (Keyboard-Video-Mouse) devices to remotely access desktops and mesh VPN services like Tailscale to connect multiple devices to a network they control despite being located across US residences. Nisos also identified the following well-known suspected operative tactics, techniques, and procedures (TTPs) during the investigation and interview, which are linked to DPRK IT workers:
Operative Details
The suspected DPRK operative applied to the Lead AI Architect role using the following PII.
- Phone: 850-308-4867
- Email address: Jo***@gmail[.]com
- Address: Palm Beach Gardens, FL 33410
- IPs: 167.88.61.250 and 167.88.61.117
Astrill VPN
The operative is likely connected to the DPRK remote hiring scheme as his IP address appears to follow common TTPs associated with DPRK IT workers. The operative used IP addresses 167.88.61.250 and 167.88.61.117 when interacting with Nisos, which likely belong to the Astrill VPN anonymization network. [1][2] Cybersecurity firms like Mandiant have published lists of IP addresses that DPRK remote workers used. Many of these IP addresses are associated with the Astrill VPN service, a popular VPN in China. [3]
VoIP Phone Number
Nisos found that phone number 850-308-4867 is likely a Voice over Internet Protocol (VoIP) number, which allowed the suspected DPRK operative to make phone calls over the internet instead of traditional phone lines. While some people use VoIP numbers as a legitimate method for contact, scammers regularly use VoIP numbers to choose phone numbers matching their applicant’s alleged location.
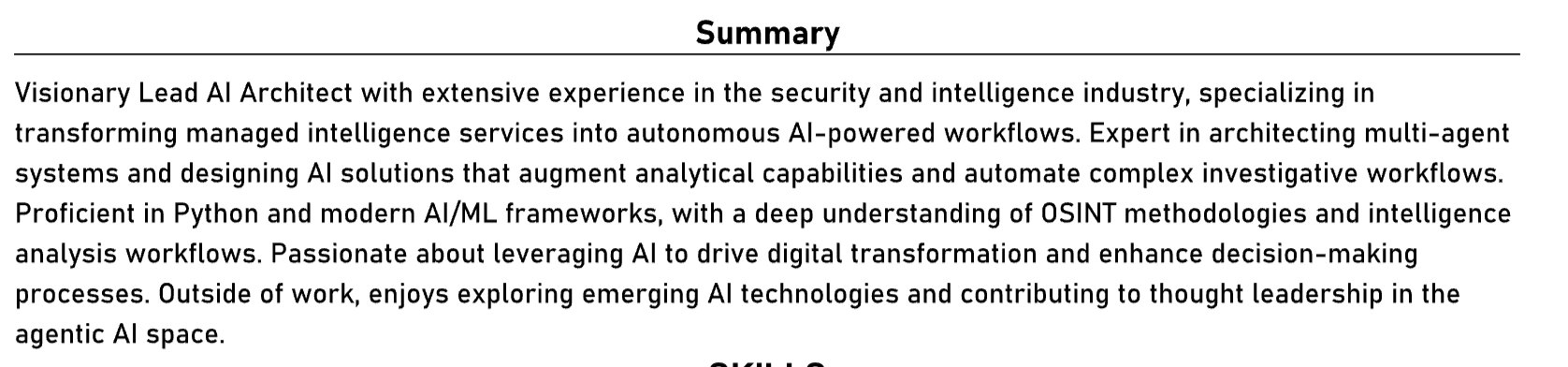
Use of AI for Resume Creation
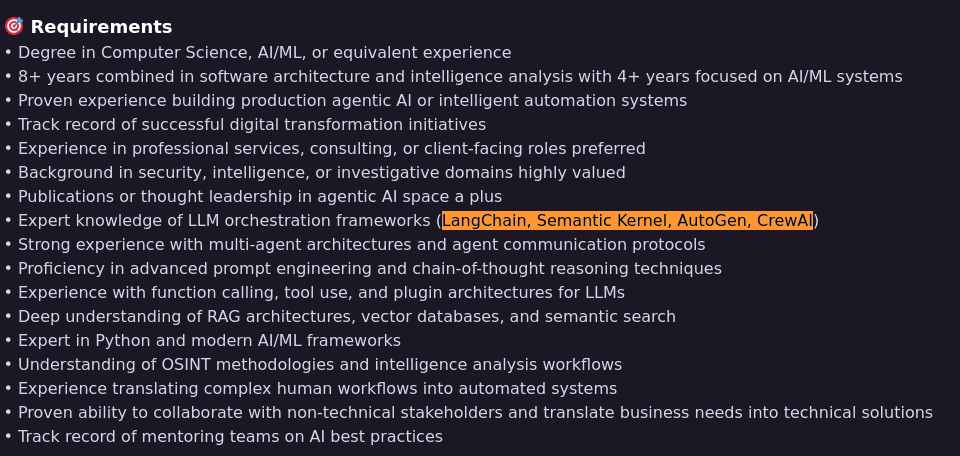
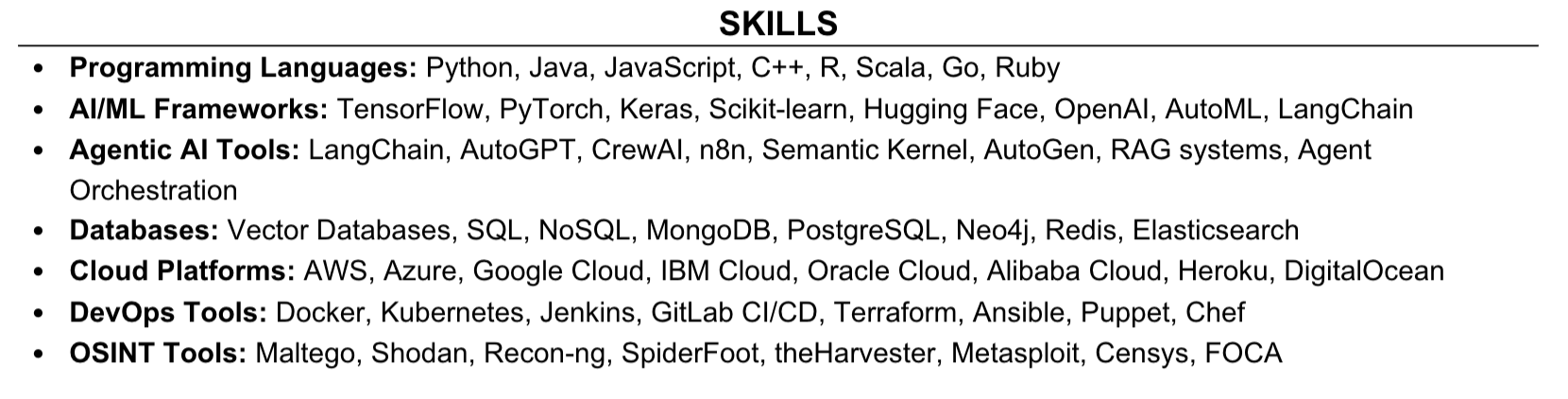
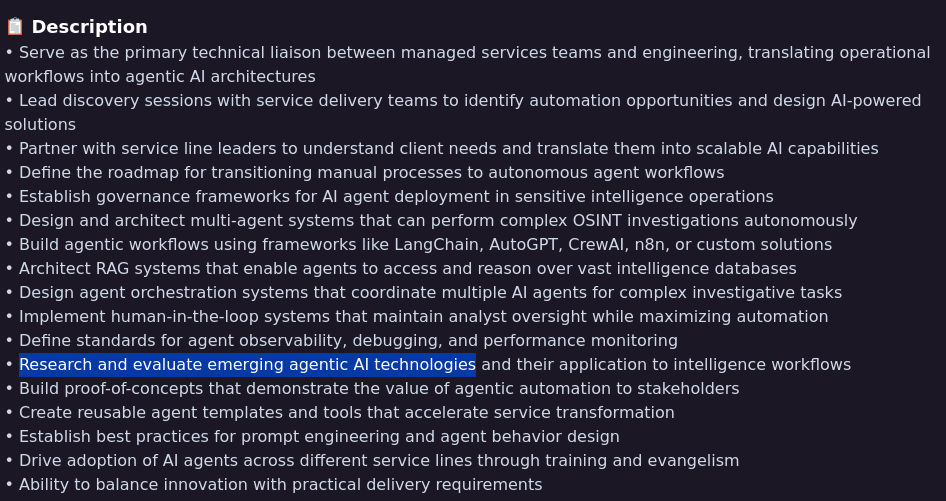
The operative likely used an AI chatbot to create his resume as the resume repeated many of the skills mentioned in the Lead AI Architect job description.
List of Skills
The suspected DPRK operative’s resume contained a list of skills, which included a number of programming languages, agentic AI tools, databases, cloud platforms and OSINT tools that he almost certainly copied from the job description. DPRK IT workers have been known to include large amounts of skills and program languages in their resumes in order to make their resumes more attractive to potential employers.
Mirrored Job Description Language
The suspected DPRK operative’s resume included a summary section, which reused content from the Lead AI Architect job description. The job description included language about researching and evaluating emerging agentic AI technologies, which the resume mirrored.
Use of Conversational AI Chatbot/Scripts for Video Interview
On 24 June 2025, Nisos conducted a virtual interview with the suspected DPRK operative. During the interview, which was conducted in English, the operative frequently looked away from the camera while answering the questions. While some of the answers could have been scripted, Nisos asked the operative a fake question about hurricane George, which supposedly impacted Florida within the last week. The operative started his reply with “How can I say?” while looking at another screen. The operative used the same phrase to start his answers to other questions that also required him to not read a script, suggesting he was waiting for the AI chatbot to provide him an answer before replying to the question.
Multiple Resume Accounts with the Same Name but Different Details
The pre-employment OSINT investigation into the suspected DPRK operative revealed three different resumes, which suggested that the operative likely set up accounts on resume platforms to gain employment as a senior full stack developer. The operative created one of the accounts in May 2025, suggesting that the persona that applied for the role at Nisos was likely a new persona. Nisos found that the resumes listed two different universities and many different employers, suggesting that the accounts and resumes were set up at different times. Of note, all resumes appear to be linked based on the true addresses of a real individual who likely had his identity stolen.
Resume Site #1
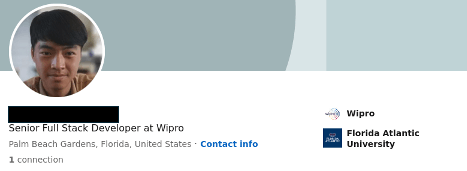
Nisos identified an account for the operative, which listed the same name, same location (Palm Beach Gardens), same university (Florida Atlantic University) and one possible previous employer (Wipro). The account however stated that the person was a full stack developer. Further research into the account showed that it was created in May 2025 and had less than five connections.
Resume Site #2
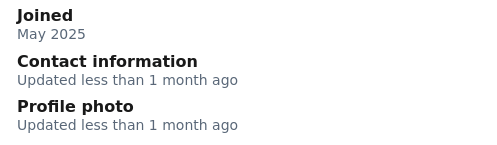
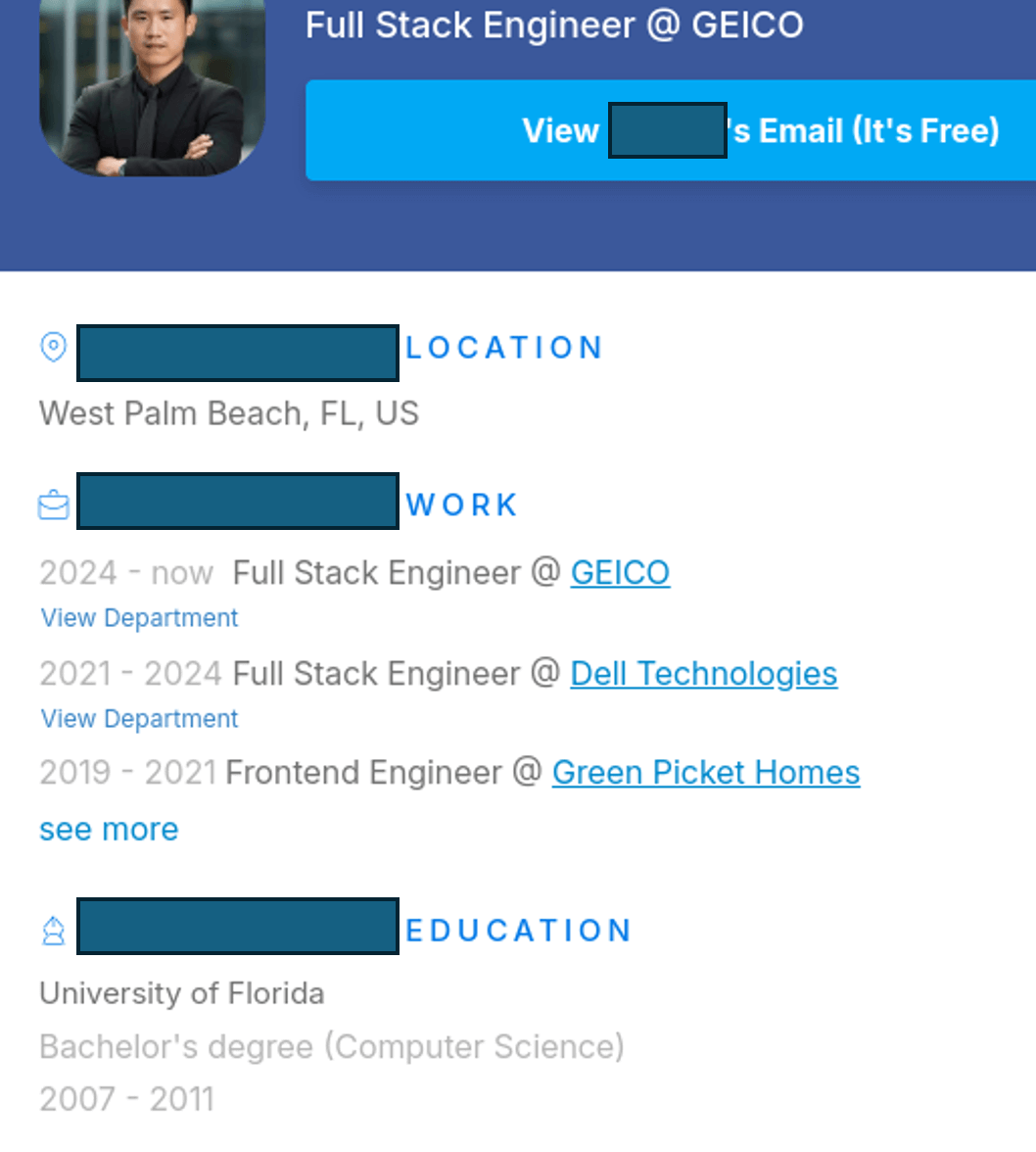
Nisos identified a second resume for the operative, which listed the same name but a different location (Greenacres), a different university (University of Florida) and different possible previous employers (Dell, Picket Homes and CVS). The resume stated that the person was also a full stack developer.
Resume Site #3
Nisos identified a third resume for the operative, which was more closely aligned with resume two above. The resume listed the same name but a different location (West Palm Beach), the same university (University of Florida) and similar possible previous employers (Geico, Dell, Green Picket Homes, and CVS). The resume stated that the person was also a full stack developer.
Nisos Research Featured in NBC News
Our investigation into North Korea’s IT worker infiltration scheme was recently covered by NBC News, highlighting the growing threat of fraudulent remote employment used to fund state-backed operations.
About Nisos®
Nisos is the human risk management company specializing in unmasking threats before they escalate. The company is a trusted advisor, operating as an extension of security, intelligence, legal, and human resource teams to protect their people and business. Nisos’ intelligence-led solutions help enterprises make critical decisions, manage human risk, and drive real world consequences for digital threats. For more information, please visit: https://www.nisos.com.